2-Factor Authentication
The second step in your defence against hackers. You'll learn how 2FA works, why it's important, the different kinds of 2FA, and how to set them up on your accounts.

In the last article in this series, we taught you how important it was to have strong, unique passwords for each of your online services.
Now, we’re going to take things one step further. For your really important accounts, we are going to get you set up with something called “2-Factor Authentication” (2FA).
You will learn:
- How 2FA works
- Why it’s important to use 2FA
- Different kinds of 2FA, their pros and cons
- How to set up 2FA on your accounts
Let’s get started.
Follow along with these resources
Download our 2FA security checklist
Easy-to-follow 2FA recommendations for skill levels ranging from “Beginner” to “Intermediate” and “Advanced.”
Take our 2FA Quiz
See how much you know already know about 2FA.
What is 2-Factor Authentication?
Two-factor authentication is an authentication method that requires two pieces of evidence to prove you are the person who should be granted access to an account. Typically, these two factors are considered to be “something you know” (your password, a PIN) and “something you have” (a smartphone, a hardware token, a security key).
Fun fact: you already use 2FA every time you visit a bank ATM to withdraw some cash. The debit card in your hand counts as “something you have” and your private PIN is “something you know.” An ATM prompts you for each of these in succession and then, should you pass the test, grants you access to your funds.
With online accounts, two-factor authentication works in a similar way:
- Enter your username and password.
- The service will ask you to authenticate with a second factor by sharing a temporary number, plugging in a security key or typing a backup code.
- You will then be granted access to your account as usual.
Why is 2FA important?
2FA offers an extra layer of security for your accounts. This is especially important for your most important accounts like email, social media, online banking, digital currency platforms, cloud file storage, and password managers.
If, for example, someone takes over your primary email account, they can reset your other account passwords. They might read and delete your emails; make online purchases in your name; steal your digital currency; blackmail or extort you; impersonate you; delete your files and backups; and, if you’re not able to regain access, lock you out of your important accounts forever.
Isn’t a password enough to protect me?
While choosing a great password is a big part of security, there are still a number of ways that bad actors can get hold of your credentials:
- Malware on your device
- Cameras that record your keystrokes
- An acquaintance or onlooker peering over your shoulder
- Man-in-the-middle attacks
- Credential stuffing
- Brute-force attacks
- Large-scale data breaches of organizations
A password simply isn’t enough anymore. You need a second factor to protect your accounts, especially since there is a real risk someone, somewhere, will try to take them over.
Digital currency users should take special care
If you are involved with digital currency in any way, you are a prime target for hackers who want to steal your digital currency. If you keep your crypto on platforms (we recommend storing digital currency in a wallet you control), you need to be especially careful.
Different types of 2-Factor Authentication
There are a handful of different types of 2-Factor Authentication that you should be aware of. Some are very insecure, some are more secure, and one stands out far above the rest. We’ll cover each of them below.
SMS and phone verification (least secure)
SMS and phone verification systems work by texting you or calling you and reading out a sequence of numbers that you then type into a website. Typically, these codes only last for a minute or two and then they expire.
The upside of this method is that it is easy to set up—you just need to provide your phone number. The downside is that SMS verification is extremely insecure if a hacker is targeting you directly.
If someone is trying to gain access to your accounts, already knows your password, and the only thing standing in their way is SMS or phone verification, there is not much you can do to stop them from doing a SIM swap attack and taking over your account.
In many cases, an attacker who does a SIM swap on your phone number can take over one of your accounts even if they don’t have that account’s password. That’s because many popular services use SMS for account recovery by default. This means your account security is, in many cases, completely dependent on the security of your phone number (i.e. not much security at all).
You can read more about SIM swapping and how to make your accounts immune to these attacks in our companion blog post: The ultimate guide to protect against SIM swap attacks.
2FA with authenticator apps (more secure)
The first secure form of 2-Factor Authentication that we recommend using is Time-based One-Time Passwords (TOTP). TOTP 2FA works with Google Authenticator (and similar apps) to generate time-based codes to use when logging in. Like with SMS verification, services will ask for your TOTP verification code after you’ve entered your username and password.
The difference here is that TOTP 2FA doesn’t require you to trust your mobile phone carrier for your account security (that is, assuming you have removed SMS verification and SMS recovery from your account).
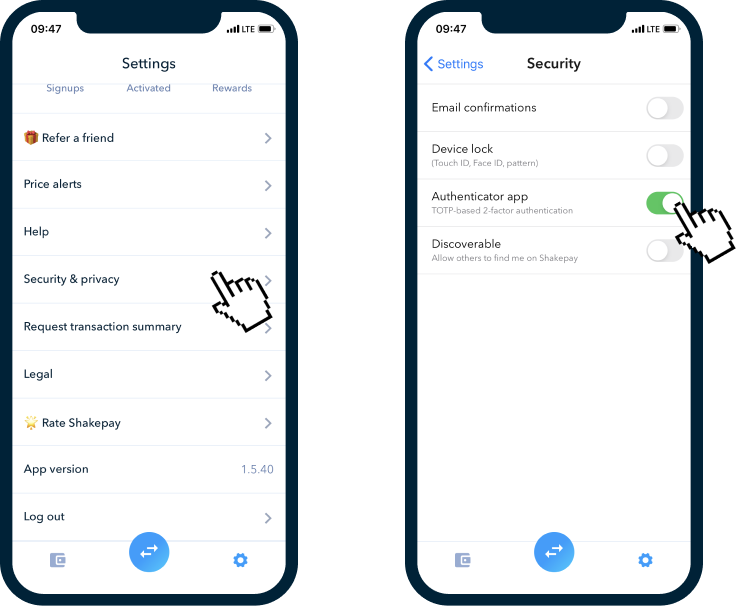
Setting up TOTP 2FA with your accounts
To set up TOTP 2FA, you will have to use Google Authenticator to scan a QR code or enter a 2FA seed (a string of letters and numbers) that has been securely transmitted to you by the service.
Your authenticator app uses this code to generate unique numbers that expire every minute or two. Having the right numbers at any particular time tells the online service you have the device where the 2FA seed was installed, making it count as “something you have.”
When prompted, you look up the numbers generated in Google Authenticator and type them into the website’s login page to finish logging in.
Be careful, TOTP is still susceptible to phishing attacks
The main drawback of TOTP 2FA is that you can still be fooled into giving away your TOTP verification code in a phishing attack.
A phishing attack will trick someone into giving away their login credentials with a fake website that looks almost exactly like the login page to a service they use.
Quick phishing demo. Would you fall for something like this? pic.twitter.com/phONMKHBle
— Mustafa Al-Bassam (@musalbas) September 9, 2018
Would you fall for this phishing email?
How phishing attacks happen
- A hacker presents you with a link to a fake login page for your service, usually in the form of a fake email or a fake ad. (Often the only way to spot these fake websites is to check its URL)
- Once you enter your login credentials on this phishing page, the hacker’s automated system will grab the login credentials you type in, including your username, password, and 2FA code.
- The hacker’s computer will then quickly log into your account on their behalf.
- The hacker now has full access to your account as if you had logged in on their computer.
- The hacker will then change your password and 2FA codes, locking you out of your own account.
What about backups?
Since TOTP apps are installed on your device, what happens if your phone gets lost, broken, or stolen?
Most of the companies we have accounts with online have a process to recover a user's account. If you can't access your 2FA authenticator, you will have to contact each company one by one and get them to confirm your identity. This can take up many days of effort if you ever lose your phone, so it’s worth backing up your TOTP codes when setting up TOTP 2FA with your accounts.
The easiest way to back things up is to screenshot and print out a copy of the QR code (or seed key) provided when setting up TOTP 2FA and then keep that in a secure location. Many services also provide eight or more one-time-use “backup codes.” These are useful backups and should also be stored in a safe place.
With backups, you should never have an issue logging into your online accounts, even if your phone is stolen, lost, or broken.
Should I use my password manager for 2FA?
Password managers like 1Password also give you the option to store your TOTP 2FA seeds in your password database so that it can act as your authenticator app.
The advantage of this is that they can generate and automatically fill in the numerical code from in your browser. These 2FA codes will also be backed up across your devices.
The drawback is that there is now a single point of failure across each of your devices for your passwords and 2FA. If someone were ever to get access to your password manager, they would also be able to access all of your accounts that use TOTP 2FA.
For most low-importance accounts, this risk is probably worth the security-to-convenience trade-off. For your most sensitive accounts (email, digital currency platforms, and so forth), we recommend you use a separate 2FA authenticator app (or rely on security keys for maximum security if that is an option).
U2F security keys (best and most secure)
Universal Second Factor (U2F) security keys are small devices that you can carry on your keychain and use as a second factor.
Unlike SMS or codes generated with a TOTP 2FA seed, they can only be validated by a single device (or whatever set of security keys you’ve pre-associated with your account). This means that they fit the bill perfectly for the second factor principle of “something you have” in addition to “something you know.”
How do security keys work?
Whenever a service asks for your second factor, you plug your Yubikey into your device and tap on its little conductive metal button to prove you are there with the device. Some Yubikeys are NFC-compatible, which means you can authenticate on your phone wirelessly by tapping your security key to the back of your phone when asked for your second factor.
The device checks the website URL that you are on and does some cryptographic wizardry to generate a validation code that it then sends back to the website you are trying to log into.
A bunch of things have to line up here to be granted access. If you have the right login credentials AND are on the right website AND have the right security key AND are there in person with the security key, you will be granted access. If you’re on a phishing website that has the wrong domain name, it simply won’t work.
Security keys are absolutely the most secure devices that you can use to validate your account with 2FA. If they’re an option, you should rely on them exclusively for your most sensitive accounts.
Security keys are the best option for 2FA
Google’s Advanced Protection Program for “anyone at risk of targeted attacks—like journalists, activists, business leaders, and political campaign teams” relies exclusively on security keys for 2FA.
In the period from mid-2017 to mid-2018, where Google had all of its 85,000 employees using security keys, the company did not see a single account takeover. Google has basically eliminated account takeovers by using security keys. This is impressive, considering how valuable it could be to have a Google employee’s credentials.
U2F security keys are faster and more secure
U2F security keys protect you against phishing by default. Also, they have been shown to be nearly four times faster to use than logging in with a TOTP authenticator app.
Lock down your most important accounts with security key 2FA
Like in Google’s program, we recommend that you use security keys to lock down your primary email address. Also be sure to remove any recovery options for your email login that have a lower level of security than this account (e.g. SMS recovery or email recovery with an email address that is less secure).
We also recommend you enable 2FA with your security key on your password manager’s online account. Here’s how you do this with 1Password.
Which security key should I choose?
When choosing a security key, you can’t go wrong with a Yubikey U2F security key. Yubikeys are quality products and are easy to set up and use. The company that makes them, Yubico, is the leader in the security key space.
Get backup security keys
As with all things, it’s important to have backups. Invest in one quality security key that you will be able to use with both your phone and your computer. Buy one or two extras to keep in a safe and/or safety deposit box in case you lose your main one.
Many hardware wallets from Ledger and Trezor also have U2F functionality built in, allowing you to use them as a security key as well.
Our 2FA recommendations
Want to tighten up your account security using 2-Factor Authentication? Explore these resources below.
Download our 2FA security checklist
Easy-to-follow 2FA recommendations for skill levels ranging from “Beginner” to “Intermediate” and “Advanced.”
Take our 2FA Quiz
See how much you've learned by re-taking our 2FA Quiz!
Thanks for reading
We hope this has been a helpful, clear, and thorough guide on 2-Factor Authentication and how to make use of it in setting up your online accounts.
In the next article, we will teach you, step-by-step, how to use Twilio and Sendgrid to create a special phone number that nobody knows so that you can forward SMS to your ultra-secure email account. This will be useful for services that don’t offer a better form of 2FA than SMS 2FA and services that require you to use a phone number for account recovery.
Further reading
Here is some extra reading on 2FA security that will help you to get even more out of this article:
What You Need to Know About SIM Swap Scams — A guide to SIM swap scams.
Man sues AT&T after fraudulent SIM swap led to $1.8M cryptocurrency theft — A 2019 article underlining the dangers of SIM swap attacks. It tells the tale of millions of dollars worth of digital currency lost to a hacker who spent less than $5,000 USD to bribe phone company employees.
Hackers Have Stolen Millions Of Dollars In Bitcoin — Using Only Phone Numbers — More on how insecure SMS 2FA really is.
Two-factor via your mobile phone – should you stop using it? — This blog post tells you what to expect if you’re ever SIM swapped and what to do (if you can do anything).
Security Advisory: Mobile Phones (Kraken) — Kraken’s classic post on locking down your email accounts and eliminating your need to trust an insecure mobile phone number for account security. Instead of using Google Voice, which is not available to Canadians, consider using Twilio with Sendgrid instead.
Choosing 2FA authenticator apps can be hard. Ars did it so you don’t have to — A guide on choosing a best TOTP 2FA app that balances security and backups.
Beyond Passwords: 2FA, U2F and Google Advanced Protection — An introduction by Troy Hunt of Have I Been Pwned to the different forms of 2-Factor Authentication available today.
How Hackers Bypass Gmail 2FA at Scale — This article shows how effective phishing can be in fooling people into typing their login credentials and time-based 2FA codes, especially when it is automated on an industrial scale. Use a U2F security key to make sure this doesn’t happen to you.
How To Add A Security Key To Your Gmail — A step-by-step guide to adding a security key to your Gmail and removing SMS as an account recovery option.
Why You Should Never Use Google Authenticator Again: Reasons why U2F is better than TOTP (one-time password) — A guide by Trezor on setting up U2F 2FA with your hardware wallet.
Bitcoin Security Made Easy: using 2-factor authentication — More on 2FA and using a hardware wallet as your U2F second factor.
Getting started with security keys — A detailed explanation of U2F security keys and how to use them.

